
A large cybercrime enterprise tracked as the "Lemon Group" has reportedly pre-installed malware known as 'Guerilla' on almost 9 million Android-based smartphones, watches, TVs, and TV boxes.
The threat actors use Guerilla to load additional payloads, intercept one-time passwords from SMS, set up a reverse proxy from the infected device, hijack WhatsApp sessions, and more.
According to a report by Trend Micro, whose analysts discovered the massive criminal enterprise and presented details about it at the recent BlackHat Asia conference, some of the attackers' infrastructure overlaps with the Triada trojan operation from 2016.
Triada was a banking trojan found pre-installed in 42 Android smartphone models from low-cost Chinese brands that sell their products globally.
Trend Micro says they first exposed the Lemon Group in February 2022, and soon after, the group allegedly rebranded under the name "Durian Cloud SMS." However, the attackers' infrastructure and tactics remained unchanged.
"While we identified a number of businesses that Lemon Group does for big data, marketing, and advertising companies, the main business involves the utilization of big data: Analyzing massive amounts of data and the corresponding characteristics of manufacturers' shipments, different advertising content obtained from different users at different times, and the hardware data with detailed software push," explains the Trend Micro report.
Implanting the malware
Trend Micro has not elaborated on how Lemon Group infects devices with the malicious firmware containing Guerilla but clarified that the devices its analysts examined had been re-flashed with new ROMs.
The analysts identified over 50 different ROMs infected with initial malware loaders, targeting various Android device vendors.
"The criminal group has infected millions of android devices, mainly mobile phones, but also smart watches, smart TVs and more," reads the description of Trend Micro's Black Hat talk.
"The infection turns these devices into mobile proxies, tools for stealing and selling SMS messages, social media and online messaging accounts and monetization via advertisements and click fraud."
Possible ways to achieve this compromise include supply chain attacks, compromised third-party software, a compromised firmware update process, or enlisting insiders on the product manufacturing or distribution chain.
Trend Micro says they initially purchased an Android phone and extracted its "ROM image" to discover the modified firmware implanted by the Lemon Group.
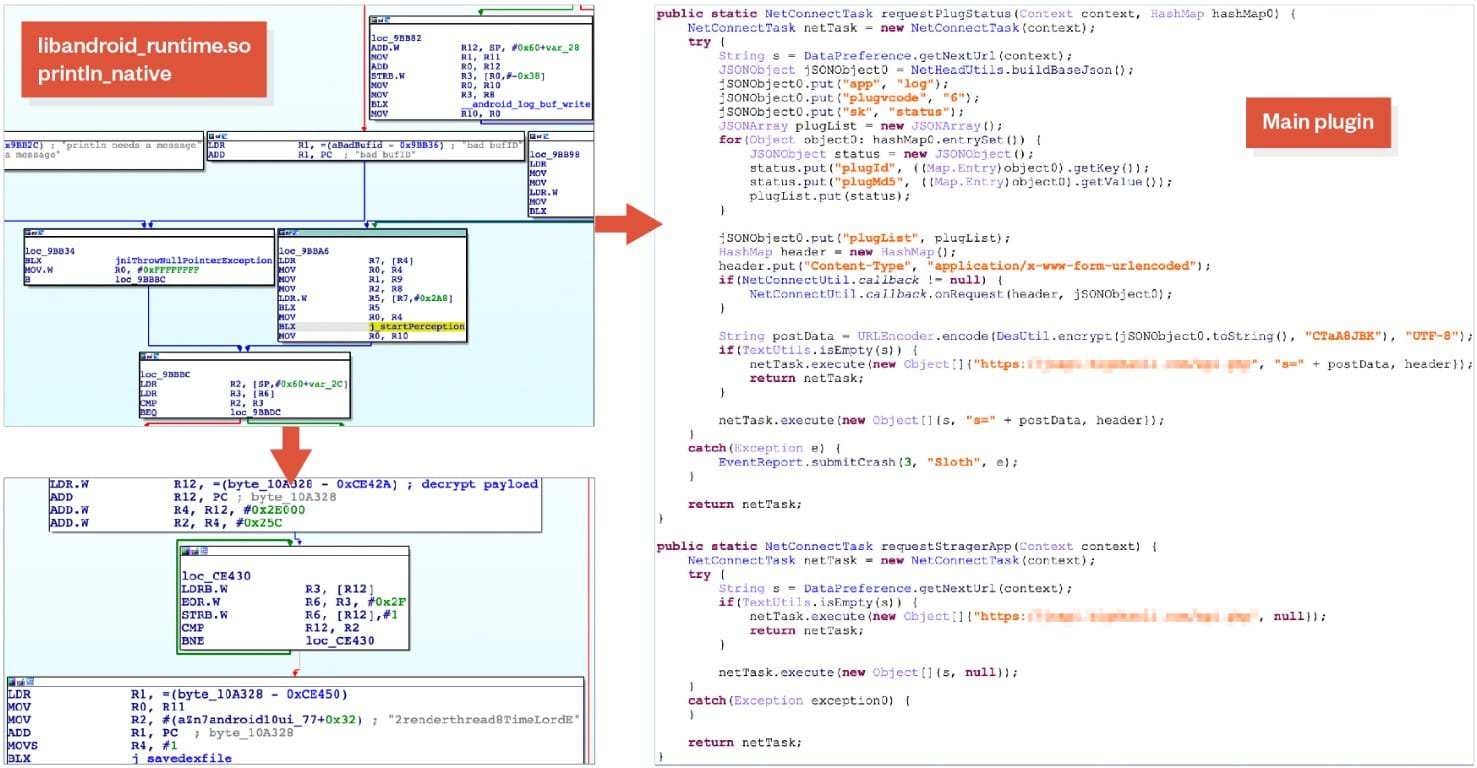
This device had a modification on the 'libandroid_runtime.so' system library to contain additional code that would decrypt and execute a DEX file.
The code of the DEX file is loaded into memory and executed by Android Runtime to activate the main plugin used by the attackers, called "Sloth," and also provide its configuration, which contains a Lemon Group domain to use for communications.
The Guerrilla malware
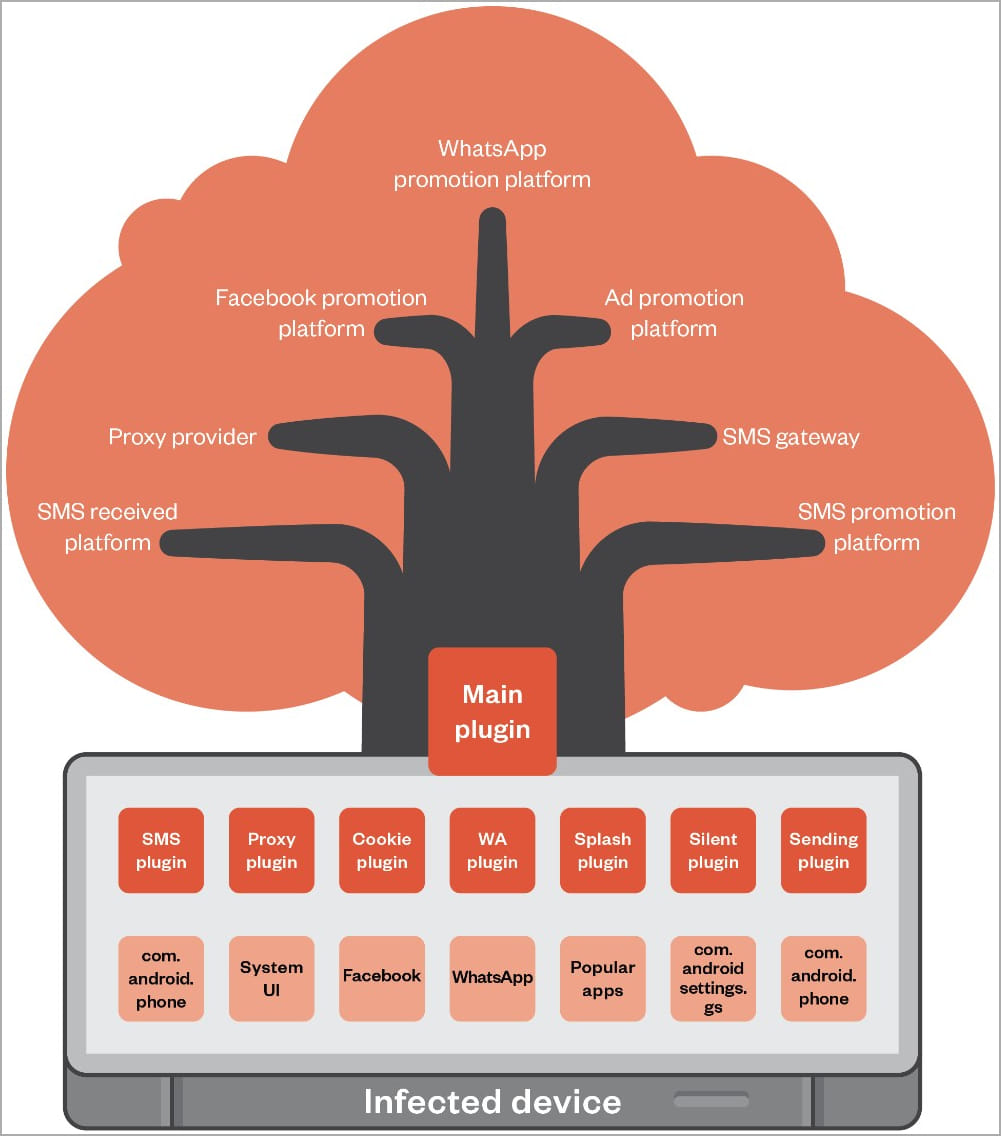
The main plugin for the Guerrilla malware loads additional plugins that are dedicated to carrying out specific functionality, including:
- SMS Plugin: Intercepts one-time passwords for WhatsApp, JingDong, and Facebook received via SMS.
- Proxy Plugin: Sets up a reverse proxy from the infected phone allowing the attackers to utilize the victim's network resources.
- Cookie Plugin: Dumps Facebook cookies from the app data directory and exfiltrates them to the C2 server. It also hijacks WhatsApp sessions to disseminate unwanted messages from the compromised device.
- Splash Plugin: Displays intrusive advertisements to the victims when they are using legitimate applications.
- Silent Plugin: Installs additional APKs received from the C2 server or uninstalls existing applications as instructed. The installation and app launch are "silent" in the sense that they take place in the background.
These functions allow the Lemon Group to establish a diverse monetization strategy that could include selling compromised accounts, hijacking network resources, offering app-installation services, generating fraudulent ad impressions, offering proxy services, and SMS Phone Verified Accounts (PVA) services.
Worldwide impact
Trend Micro reports that Lemon Group had previously claimed on its service-offering site to control nearly nine million devices spread across 180 countries. The countries most significantly impacted include the United States, Mexico, Indonesia, Thailand, and Russia.
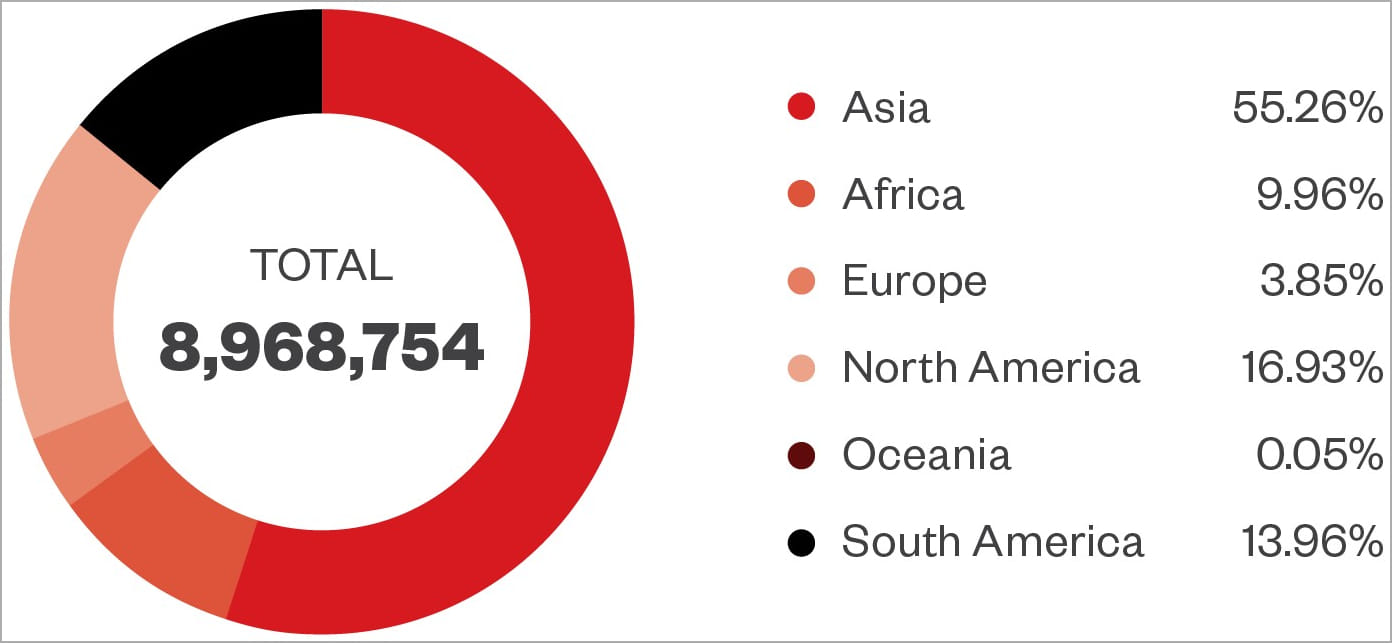
"Further, through our telemetry data, we confirmed that there are millions of infected devices operated globally. The main cluster of these devices is in South-East Asia and Eastern Europe, however, this is a truly global problem," said Trend Micro.
Trend Micro suggests that the actual count of Android devices infected with Guerrilla could be higher. However, those devices have not yet communicated with the attackers' command and control servers because they are still awaiting purchase.
By monitoring the operation, the analysts detected over 490,000 mobile numbers used for generating one-time password requests for SMS PVA services from JingDong, WhatsApp, Facebook, QQ, Line, Tinder, and other platforms.
The identification of over half a million compromised devices tied to just a single service offered by this cybercrime syndicate signifies a substantial global reach of their malicious operations.
BleepingComputer has asked Trend Micro where they purchased the pre-infected phone, how it's being sold, and what brands are impacted, but a reply was not immediately available.











No comments:
Post a Comment